The Most Common Entry Points for Ransomware in Businesses
Mitch Wolverton
Ransomware attacks have become one of the most disruptive cyber threats facing organizations today. Businesses of all sizes are targeted by attackers seeking to encrypt data, disrupt operations, and demand payment in exchange for restoring access. The financial impact of ransomware continues to grow, and the operational consequences can be even more severe when systems remain unavailable for extended periods.
To defend against these attacks, organizations must understand how attackers gain access to their systems in the first place. Identifying the Most Common Entry Points for Ransomware allows businesses to strengthen their defenses and reduce the likelihood of an incident.
This article explores the Most Common Entry Points for Ransomware, explains how attackers exploit them, and outlines practical strategies organizations can use to reduce risk.
Why Understanding Ransomware Entry Points Matters
Ransomware attacks rarely begin with a dramatic system takeover. In most cases, attackers gain access through a relatively simple vulnerability. Once inside the network, they escalate privileges, move laterally through systems, and deploy ransomware after they have reached critical infrastructure.
According to the Cybersecurity and Infrastructure Security Agency (CISA), ransomware groups often rely on basic security weaknesses rather than advanced hacking techniques. Many attacks succeed because organizations lack strong authentication controls, fail to patch vulnerabilities, or allow employees to unknowingly interact with malicious content. Information published by CISA highlights how ransomware operators frequently exploit exposed remote access services and phishing emails to initiate attacks.
Understanding the Most Common Entry Points for Ransomware allows organizations to focus their cybersecurity efforts on the areas that matter most.
Phishing Emails
Phishing emails remain one of the Most Common Entry Points for Ransomware. Attackers craft messages that appear to come from trusted sources such as vendors, coworkers, financial institutions, or cloud platforms.
These emails often contain:
- Malicious attachments disguised as invoices or documents
- Links that redirect users to credential harvesting websites
- Files that download malware when opened
Once a user clicks a link or opens an attachment, malware may install itself on the device. This malware can create a backdoor that allows attackers to access the network.
Organizations reduce phishing risk by implementing:
- Security awareness training
- Email filtering and threat detection tools
- Multi factor authentication for critical systems
Employee education remains one of the most effective defenses against phishing based ransomware attacks.
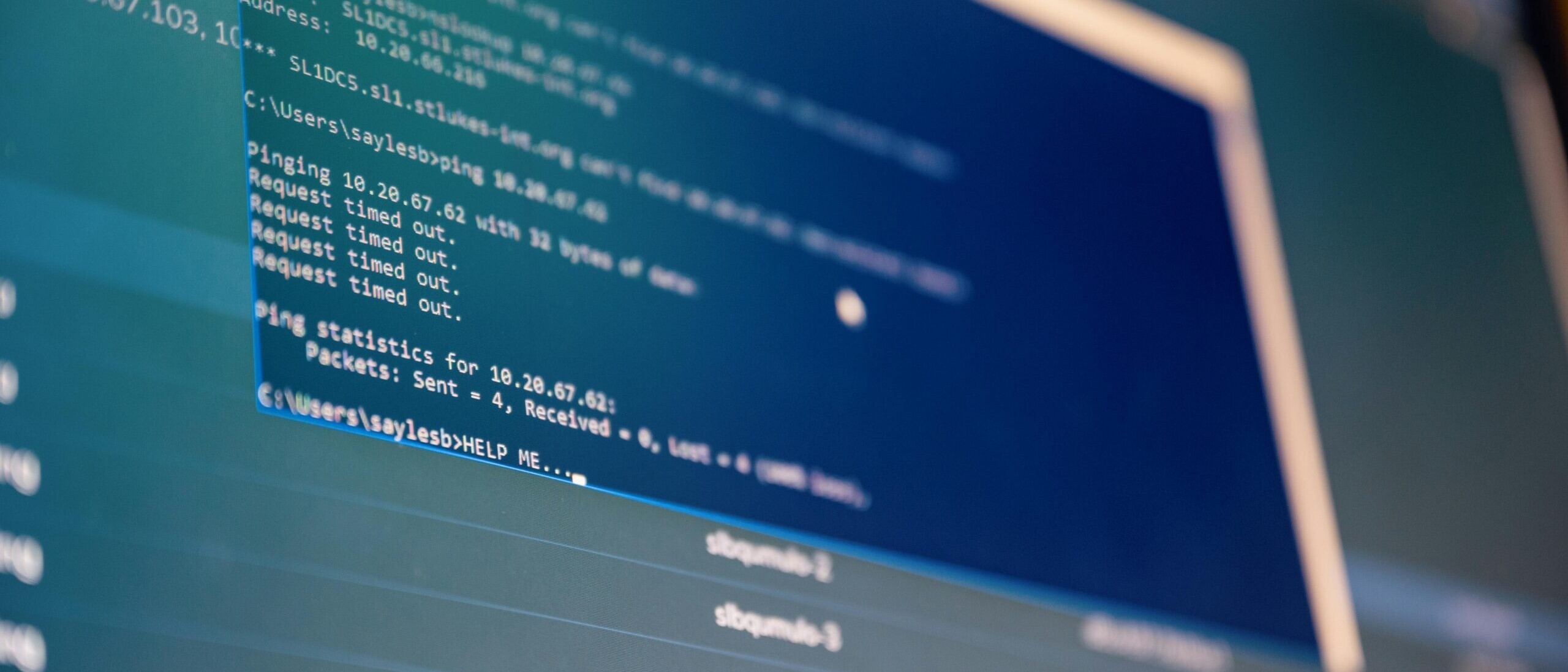
Remote Desktop Protocol (RDP) Exposure
Another of the Most Common Entry Points for Ransomware involves exposed remote access services such as Remote Desktop Protocol. RDP allows users to connect to computers remotely and is widely used for system administration and remote work.
When RDP services are exposed directly to the internet without strong authentication controls, attackers can attempt to gain access using automated password guessing tools.
Once access is obtained, attackers can:
- Install ransomware directly
- Disable security tools
- Move through the network to access servers and backups
CISA has repeatedly warned that improperly secured RDP services remain a major cause of ransomware incidents.
Organizations can reduce this risk by:
- Disabling RDP when it is not required
- Restricting remote access using VPNs
- Implementing multi factor authentication
- Monitoring login attempts and unusual access activity
Properly securing remote access services significantly reduces the risk of ransomware infiltration.
Unpatched Software Vulnerabilities
Software vulnerabilities are another major contributor to the Most Common Entry Points for Ransomware. Attackers actively scan the internet for systems running outdated software that contains known security flaws.
When vulnerabilities are discovered, attackers may exploit them to gain unauthorized access to servers, workstations, or network devices.
Examples include vulnerabilities in:
- Operating systems
- Web servers
- VPN appliances
- Firewall devices
- Business applications
Once a vulnerability is exploited, attackers may install malware that allows them to control the affected system.
Organizations reduce this risk by implementing structured patch management processes. This includes regularly updating software, monitoring vendor security bulletins, and applying critical patches as soon as possible.
According to guidance from NIST, timely patching remains one of the most effective ways to prevent cyberattacks that exploit known vulnerabilities.
Compromised Credentials
Compromised usernames and passwords are another of the Most Common Entry Points for Ransomware. Attackers often obtain credentials through phishing campaigns, data breaches, or password reuse across multiple platforms.
Once credentials are obtained, attackers may log into systems without triggering security alerts. This allows them to explore the network while appearing to be legitimate users.
Credential based attacks often involve:
- Password spraying
- Credential stuffing
- Reuse of previously leaked passwords
When accounts lack multi factor authentication, the risk increases significantly.
Organizations should adopt several best practices to protect against credential theft:
- Implement multi factor authentication across all critical systems
- Enforce strong password policies
- Monitor for unusual login patterns
- Use identity protection tools that detect suspicious access behavior
Protecting user credentials is a critical step in preventing ransomware attacks.
Malicious Downloads and Drive by Attacks
Another pathway within the Most Common Entry Points for Ransomware involves malicious downloads or compromised websites. In these scenarios, users may unknowingly download malware while browsing the internet.
This can occur when:
- Visiting compromised websites
- Downloading pirated software
- Installing unauthorized browser extensions
- Interacting with malicious advertisements
Once malware is downloaded, attackers may gain a foothold inside the network.
Organizations can reduce this risk by implementing:
- Web filtering tools
- Application control policies
- Endpoint protection platforms
- Restrictions on unauthorized software installation
These controls prevent users from unintentionally introducing ransomware into the environment.
Third Party and Supply Chain Access
The final category among the Most Common Entry Points for Ransomware involves third party access. Many organizations rely on vendors, contractors, and service providers who require access to internal systems.
If one of these external partners is compromised, attackers may use that relationship to gain entry into the network.
Supply chain attacks have become increasingly common because attackers can compromise multiple organizations through a single vulnerable vendor.
Organizations should carefully manage vendor access by:
- Limiting privileges for third party accounts
- Monitoring external access activity
- Implementing strong authentication requirements
- Reviewing vendor security practices
Supply chain risk management is now a critical component of modern cybersecurity strategies.
Strengthening Defenses Against Ransomware
While the Most Common Entry Points for Ransomware may vary between organizations, the underlying lesson remains the same. Most ransomware incidents begin with preventable weaknesses.
Businesses can significantly reduce risk by focusing on several foundational cybersecurity practices:
- Implement multi factor authentication across all systems
- Maintain consistent patch management programs
- Train employees to recognize phishing attempts
- Restrict remote access services
- Monitor networks for unusual activity
- Maintain secure and tested data backups
Organizations that adopt proactive security strategies are far less likely to experience successful ransomware attacks.
The Role of Managed Security Services
Defending against ransomware requires continuous monitoring, rapid response capabilities, and a deep understanding of evolving cyber threats. Many organizations lack the internal resources to manage these responsibilities effectively.
Managed service providers can help businesses strengthen their defenses by delivering services such as:
- 24/7 security monitoring
- vulnerability management
- endpoint protection
- threat detection and response
- identity and access management
By partnering with cybersecurity specialists, businesses gain access to expertise and tools that reduce exposure to ransomware attacks.
Final Thoughts
Ransomware remains one of the most serious threats facing organizations today, but most successful attacks rely on predictable weaknesses. Understanding the Most Common Entry Points for Ransomware allows businesses to take targeted steps that significantly reduce risk.
Phishing emails, exposed remote access systems, unpatched vulnerabilities, compromised credentials, malicious downloads, and supply chain access all represent common attack vectors used by ransomware operators.
By addressing these vulnerabilities and adopting proactive cybersecurity practices, organizations can protect their systems, safeguard their data, and maintain business continuity in an increasingly hostile digital environment.
Mitch Wolverton
Mitch, Marketing Manager at PivIT Strategy, brings over many years of marketing and content creation experience to the company. He began his career as a content writer and strategist, honing his skills on some of the industry’s largest websites, before advancing to specialize in SEO and digital marketing at PivIT Strategy.
